How AI & LSTM Models Detect Cyber Threats in Real Time
Cyber attacks don’t wait they evolve every hour. Modern threats such as phishing, malware, and network intrusions are becoming increasingly sophisticated, making them difficult to detect with traditional cybersecurity tools.
Artificial Intelligence (AI) and Machine Learning (ML) are revolutionizing threat detection by learning patterns from large datasets and identifying suspicious behavior instantly. One of the most effective models for this task is the Long Short-Term Memory (LSTM) network, which specializes in analyzing time-based data like network logs and user activity sequences.
This article explains how LSTM models work in cybersecurity and shows you how to build a (practical threat detection pipeline step by step.
Why Traditional Security Tools Struggle Today
Rule-based systems and signature scanners are great for known threats. But modern attacks:
- Change their patterns frequently
- Hide inside normal traffic
- Unfold slowly over time (low-and-slow attacks)
These tools often miss behavioral anomalies. ML models, by contrast, learn what “normal” looks like and flag deviations.
Where AI Fits in Cybersecurity
AI/ML can help with:
| Use Case | What AI Learns | What It Flags |
| Network anomaly detection | Normal traffic rhythms | Spikes, odd sequences |
| Login behavior analysis | Usual user patterns | Suspicious access attempts |
| Phishing detection | Email/text patterns | Malicious intent |
| Malware detection | System activity traces | Abnormal execution paths |
The common thread? Time-ordered data. That’s LSTM’s sweet spot.
What Is LSTM and Why It’s Perfect for Security Data?
Long Short-Term Memory is a type of recurrent neural network built to remember long sequences without “forgetting” earlier context.
Security data is sequential:
- Packets over time
- Keystrokes and logins over time
- Process calls over time
LSTM learns temporal dependencies:
“After pattern A and B, pattern C is normal… but D is suspicious.”
Architecture: LSTM for Threat Detection
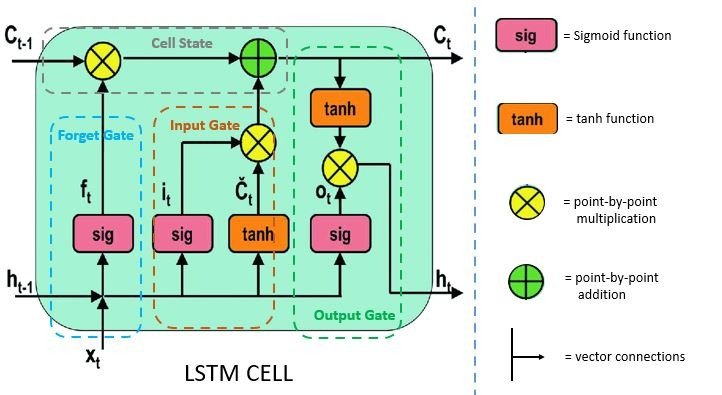
Pipeline overview:
- Collect logs (network / system / auth)
- Convert to time-series features
- Feed sequences into LSTM
- Model predicts: normal vs anomaly
- Trigger alert if anomaly score crosses threshold
Step-by-Step: Build a Simple LSTM Threat Detector
1) Dataset Ideas
Use public datasets such as:
- NSL-KDD
- CIC-IDS2017
- UNSW-NB15
These include labeled normal and attack traffic.
2) Feature Engineering
Turn raw logs into sequences:
- Packet size
- Protocol
- Duration
- Failed login count
- Time between requests
Normalize and create sliding windows (e.g., 20–50 timesteps).
3) Model (concept)
model = Sequential()
model.add(LSTM(64, input_shape=(timesteps, features), return_sequences=True))
model.add(LSTM(32))
model.add(Dense(1, activation=’sigmoid’))
4) Train
- Loss: binary cross-entropy
- Metric: accuracy, recall (very important for attacks)
- Handle class imbalance (attacks are rare)
5) Evaluate
Focus on:
- Recall (catch attacks)
- False positives (don’t spam alerts)
Real-World Applications
| Scenario | What LSTM Detects |
| Insider threat | Unusual access sequence |
| DDoS | Traffic rhythm shift |
| Brute force | Repeated timed failures |
| Data exfiltration | Slow abnormal transfers |
Security teams can plug this into a Security Operations Center (SOC) alert pipeline.
Challenges You Must Handle
- Imbalanced data (few attacks)
- Noisy logs
- Concept drift (behavior changes over time)
- Need for retraining with fresh data
Tools & Stack
- Python, NumPy, Pandas
- TensorFlow / Keras
- Scikit-learn for preprocessing
- Matplotlib for visualization
Future of AI in Cybersecurity
Expect:
- Real-time streaming LSTM models
- Hybrid models (LSTM + Transformers)
- AI copilots for SOC analysts
- Self-healing networks that auto-block anomalies
Conclusion
AI is no longer optional in cybersecurity. With LSTM models, you can move from reactive defense to predictive protection by learning how behavior unfolds over time.If you’re a student or fresher, building even a small LSTM-based anomaly detector is a standout project that proves you understand both AI and security in practice.

Subscribe to Our Newsletter!
Get The Latest News, Updates, And Amazing Offers
Popular Posts
Apr 8, 2026
How to Build a UI/UX Portfolio With Zero Experience
Apr 1, 2026
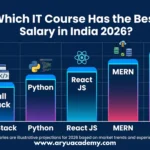
Which IT Course Has the Best Salary in India2026?

Mar 24, 2026
Python Course After 12th: Scope,Salary & Career Roadmap in 2025